I appreciate your measures to improve security.
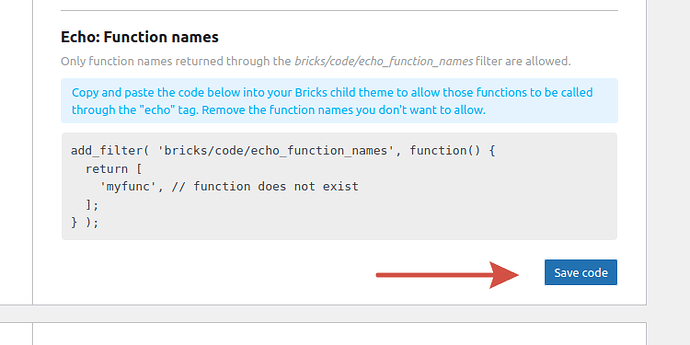
However, the echo function name filter “bricks/code/echo_function_names” is, in my humble opinion, not the best approach.
I use PHP function calls a lot in my projects, especially with custom functions.
Since the new filter only allows to return exact function names, I have to keep a second window open to frequently update my snippet containing the filter. (I’m using a code snippet instead of functions.php of a child theme)
A better solution would be to e.g.
a) allow function name wildcard patterns
b) allow functions in defined PHP namespaces
An external attacker wouldn’t be able to guess my pattern or namespace.
So this solution would be as safe as defining exact function names.
[EDIT]
Ideas from the related post in the FB group (Redirecting...):
-
Pass the function name as parameter to the filter so we can implement our own filter algorithm/rules (for example, allow functions by patterns like projectname_, get_, \namespace.…).
-
Allow disabling the filter during development and show a red flag instead. We can then run the code review and add the whitelist after finishing development.
-
Red flag for {echo:} using functions not whitelisted, so we don’t spend time wondering why we don’t get the expected output